A developer shipped a pull request on a Friday afternoon. Buried in the diff was an exposed AWS key. The existing scanner did not flag it until Monday, after the code had been merged, deployed, and the key had been active in production for 60+ hours. The remediation took a full sprint: key rotation, audit trail review, incident report, compliance paperwork.
One developer told me during research: 'By the time security tools tell me something is wrong, it is already a fire drill.' I designed SecureFlow to end this pattern. A GitHub-native plugin that catches secrets in real time during pull requests, with inline remediation, contextual explanations, and team-level dashboards, all without pulling developers out of their workflow.
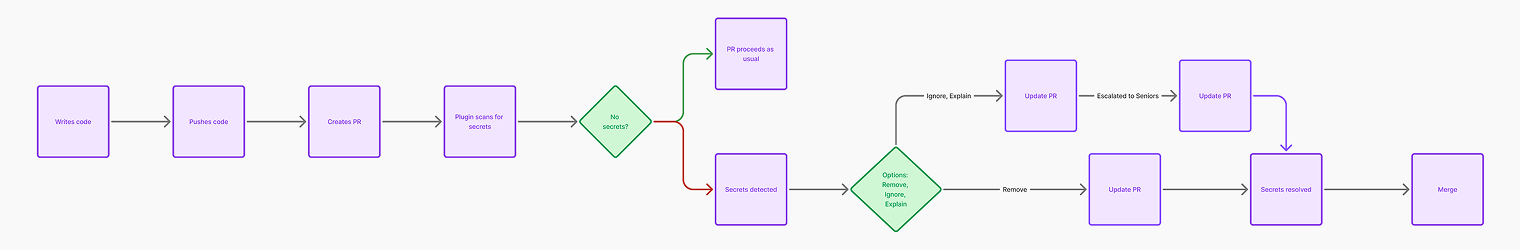
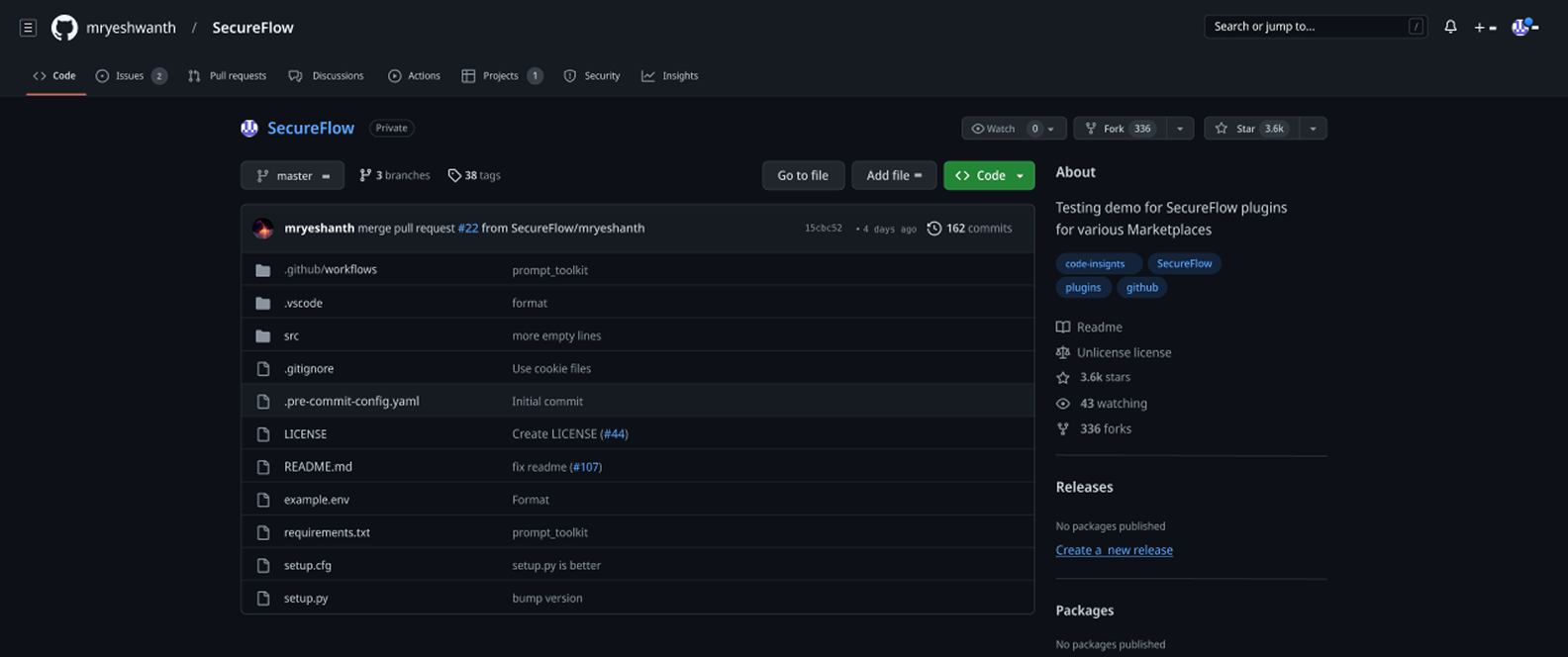
SecureFlow works entirely inside GitHub's PR workflow. When a developer opens a pull request, the plugin scans the diff, surfaces secrets inline, and provides one-click remediation. For team leads, a dedicated dashboard highlights recurring patterns, high-risk contributors, and audit trails. The core design principle: zero context switching, zero external tools, zero workflow interruption.
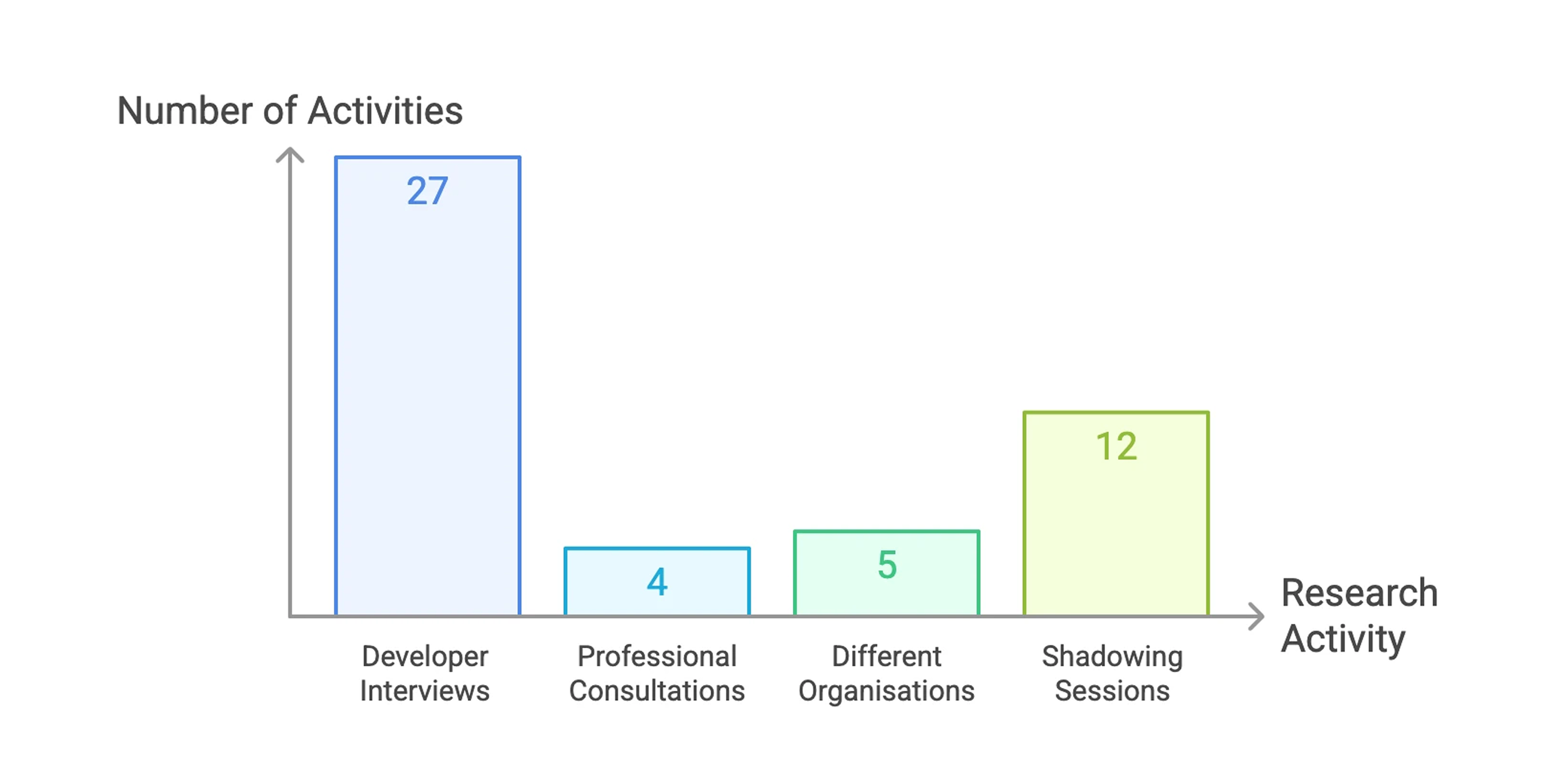
I led this project end-to-end over 1 month, from research through the final GitHub-native PR experience and team dashboards. I worked with 3 engineers, 1 PM, and the engineering lead on detection logic and API feasibility. Key decisions, like inline remediation over external dashboards, coaching-based escalation over punitive alerts, and a 2-minute PR resolution threshold, were mine to make and validate through research.
SecureFlow improved security posture without compromising developer speed.
42% reduction in unresolved secrets
32% reduction in false positive alerts
17% reduction in pull request review time (from an average of 8 minutes to 6.5 minutes per PR)
50% reduction in security-related rollbacks
The problem was timing, not intent. Developers were not ignoring security. They were shipping code without any signal that credentials were exposed. By the time existing scanners caught the issue, the code had already been merged or deployed, triggering expensive remediation cycles and repeated incidents that eroded trust in security tooling.
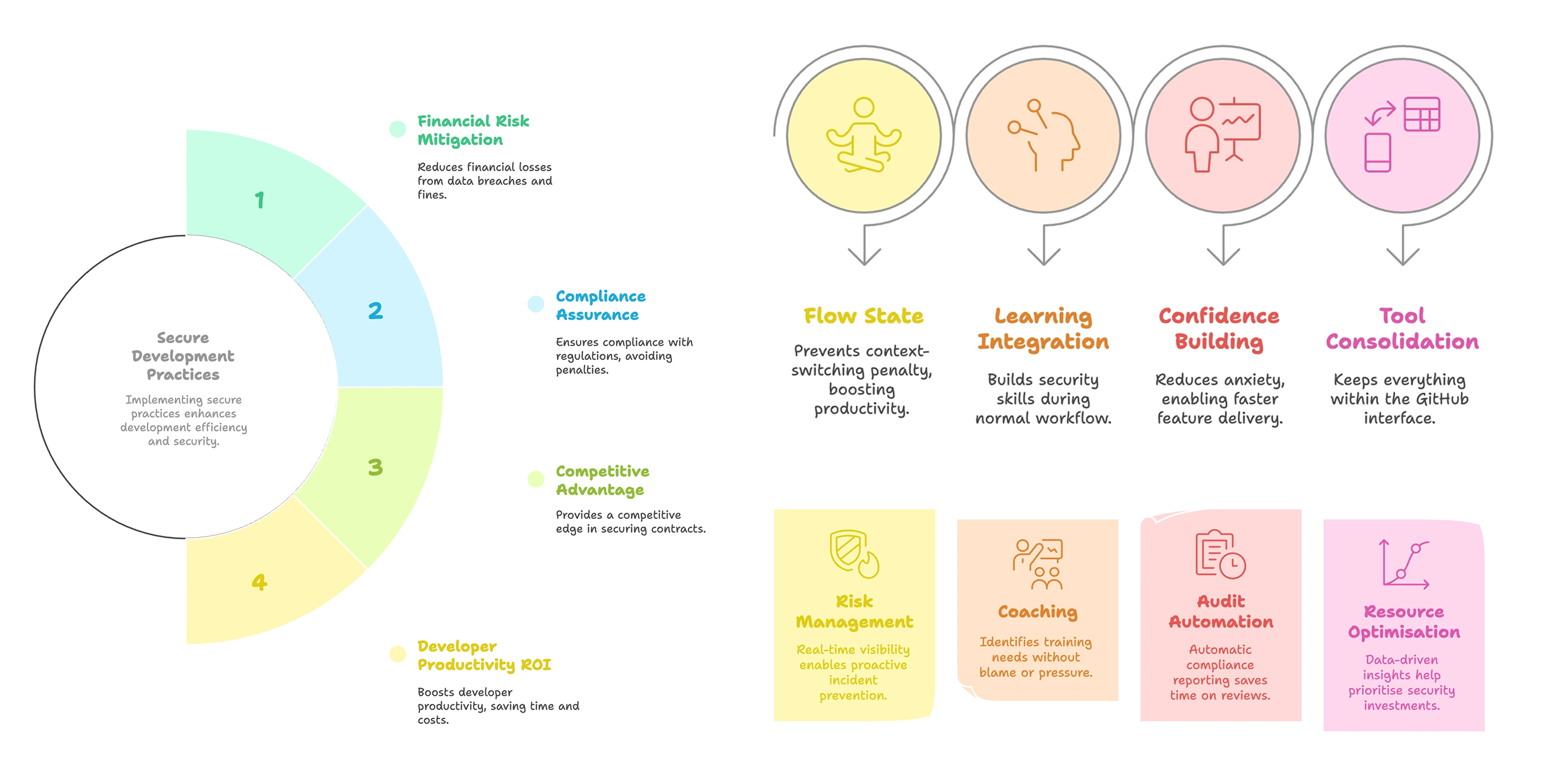
The security tooling landscape was fragmented. Most products offered scanning but not workflow-native experiences. Developers wanted speed and accuracy. Security leads wanted visibility into recurring risks. I mapped these needs against existing tools and found no product satisfied all three. SecureFlow was designed to close that gap by embedding intelligence where code is reviewed.

Prevent leaks early, reduce compliance failures, and avoid costly post-production fixes.
Get accurate, contextual alerts without switching tools or losing momentum.
See patterns, high-risk behaviours, and bottlenecks with actionable insights without needing to micromanage.
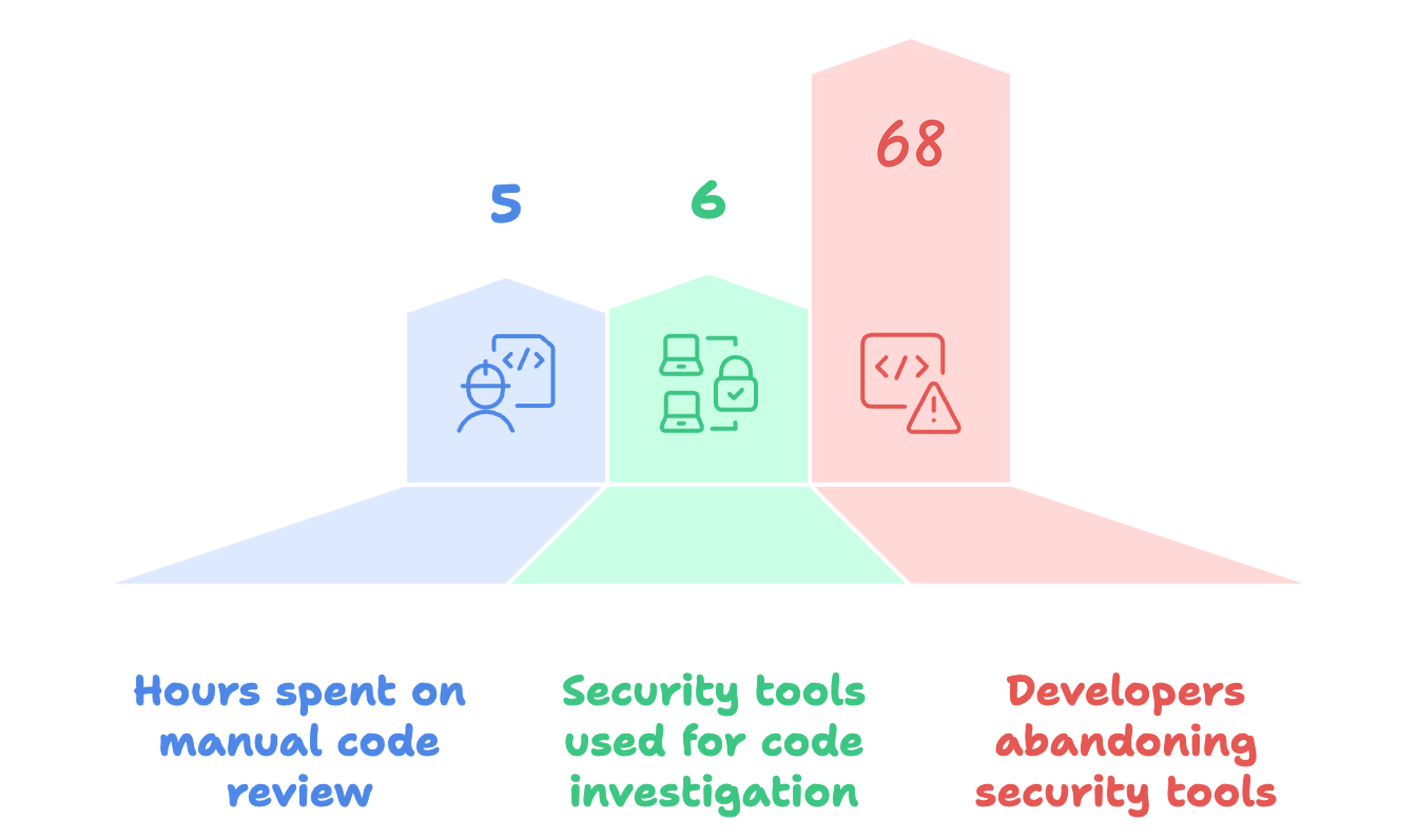
I interviewed 6 developers and 3 team leads (with PM support) and shadowed workflows across 2 sprint cycles over 2 weeks. The frustrations were consistent: 'I stopped looking at security alerts because 80% are noise' (senior developer). 'By the time I find out about a leaked secret, I have already context-switched three times' (team lead). Developers abandoned tools that interrupted flow. False positives had eroded trust in automated alerts. Post-merge scanning made every fix a costly context switch. These insights validated that real-time, in-flow detection was the only viable direction.
Most competing tools operated post-merge, relied on external dashboards, and generated excessive noise. Developers dismissed them as workflow blockers. Team leads had no visibility into repeated mistakes across their teams. The design opportunity became clear: build a context-aware, GitHub-native experience that works where developers already work, not alongside it.
These gaps became the backbone of SecureFlow's features.
"When I create a pull request, I want real-time, high-accuracy secret detection inside GitHub so I can fix issues quickly."
"When security issues repeat, I want visibility into patterns so I can coach my team and maintain compliance."
SecureFlow integrates directly into GitHub pull requests with inline scanning, contextual alerts, and one-click remediation. Developers stay inside GitHub; team leads get dashboards highlighting patterns and risks; organizations gain automated audit trails.
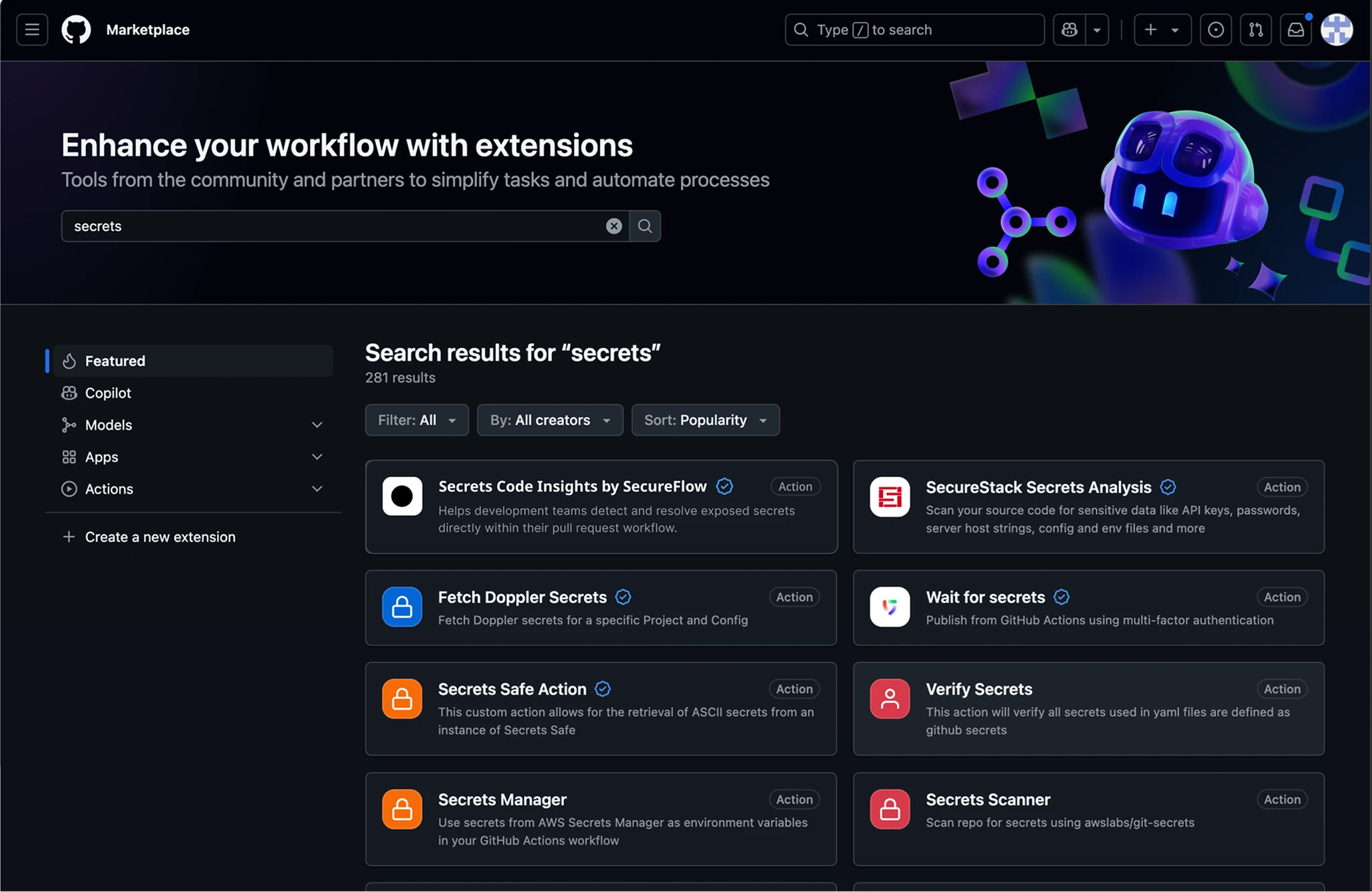
Installation happens via GitHub Marketplace. The plugin's positioning clearly communicates its frictionless, GitHub-native workflow, addressing the top reason developers abandoned previous tools.
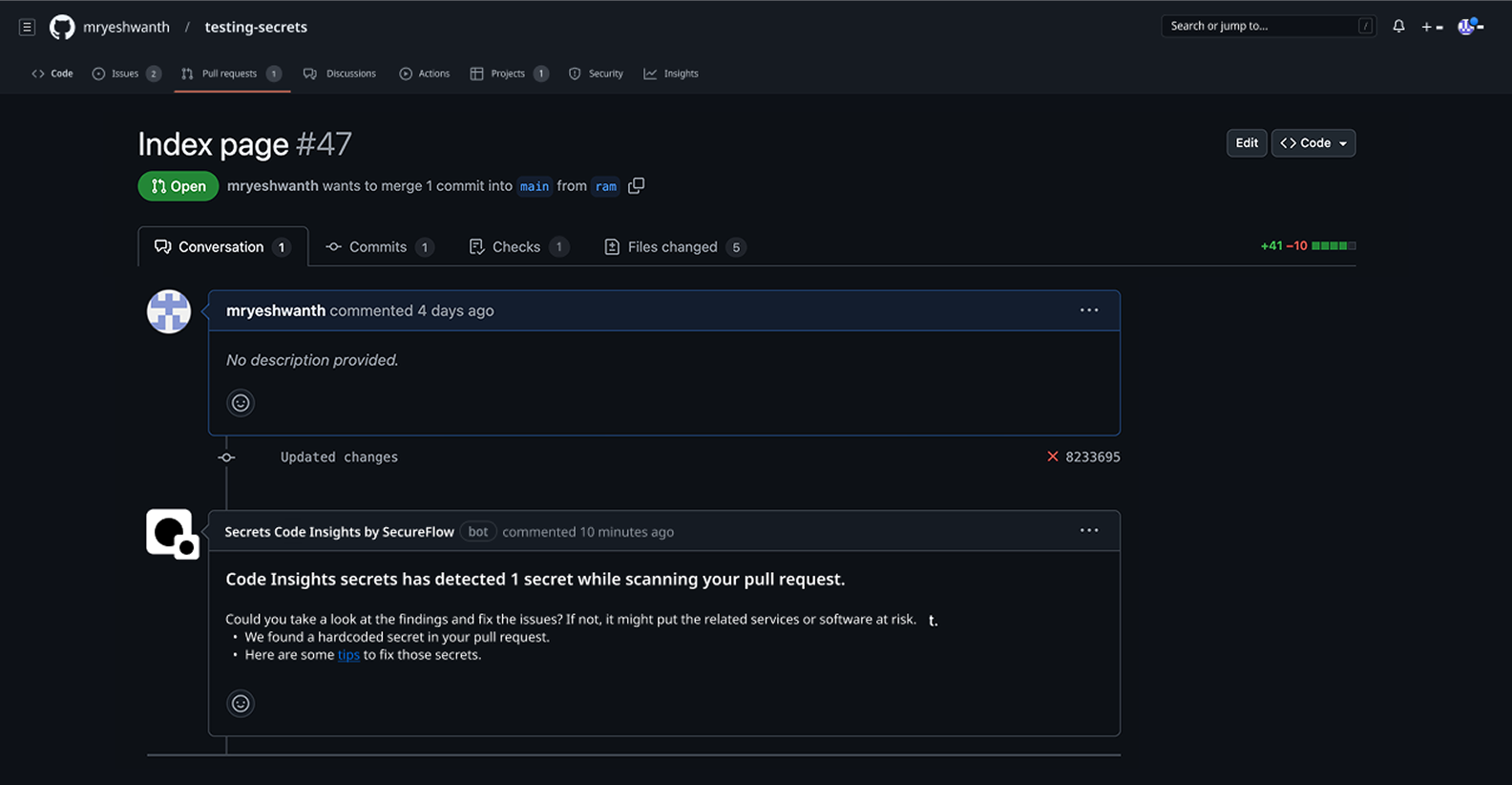
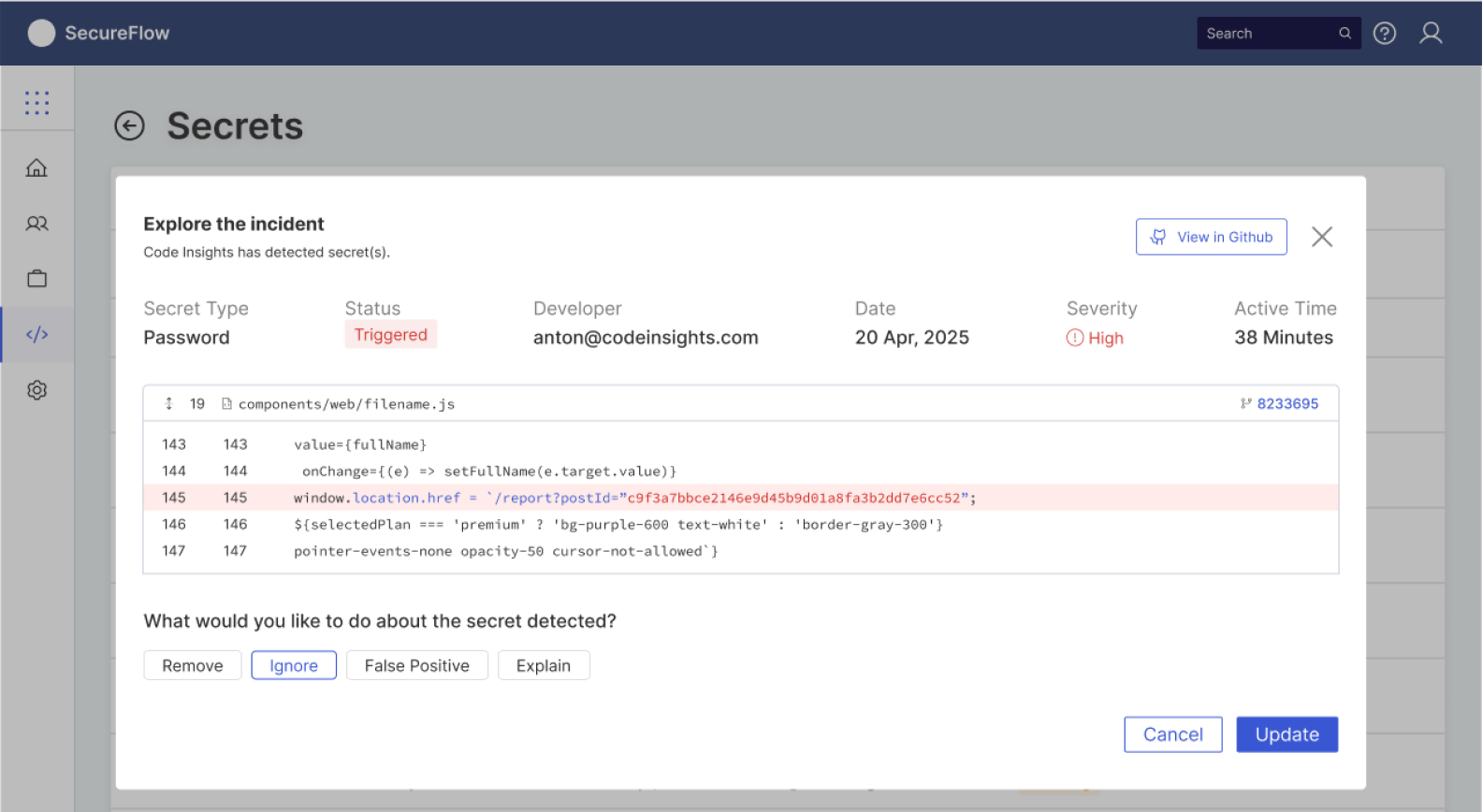
When a PR is opened, SecureFlow scans the diff instantly.
If clean: a green check and "safe to merge."
If issues exist: inline annotations appear next to the risky lines.
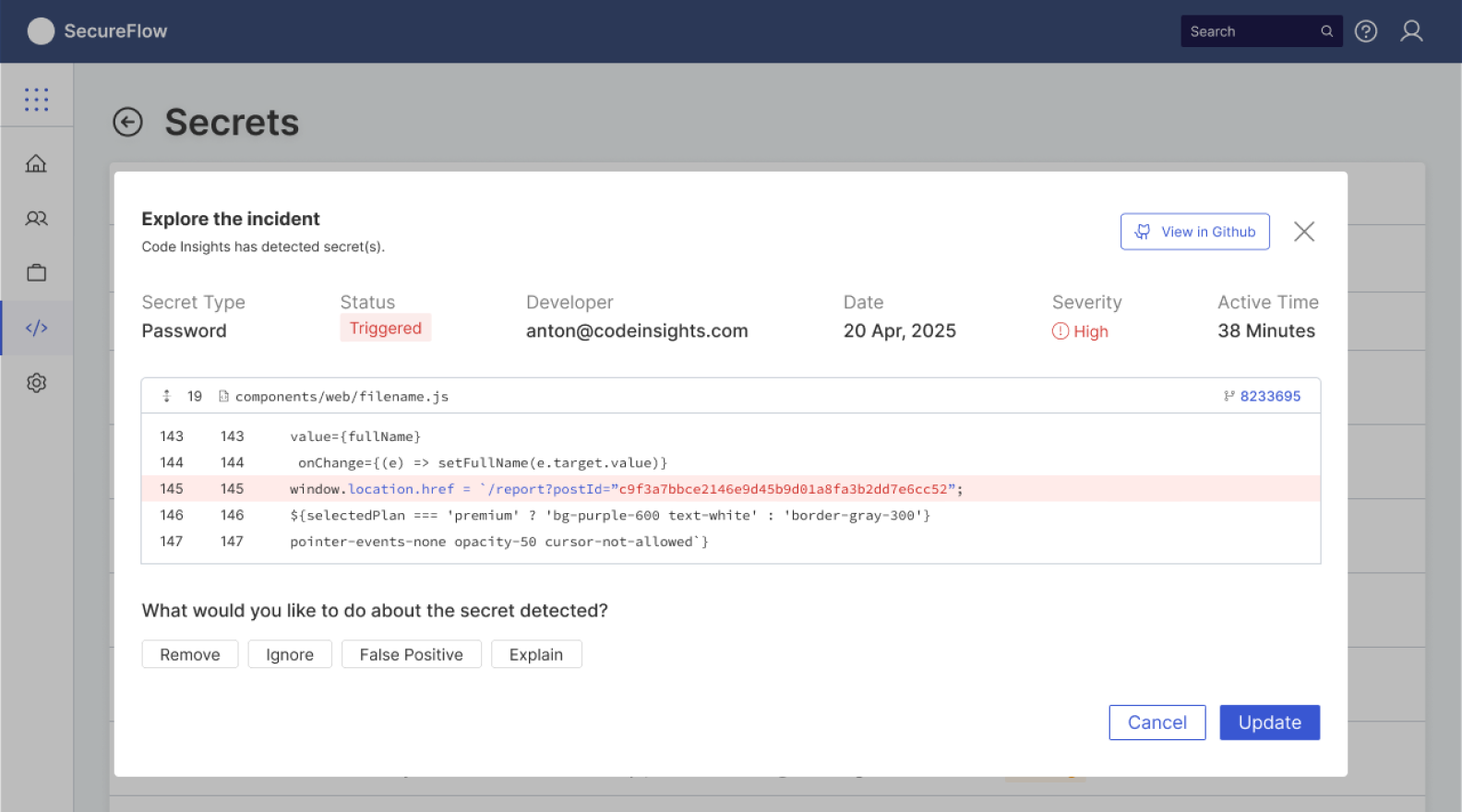
Developers can immediately Remove, Ignore, Mark as False Positive, or Request Explanation, all without leaving GitHub.
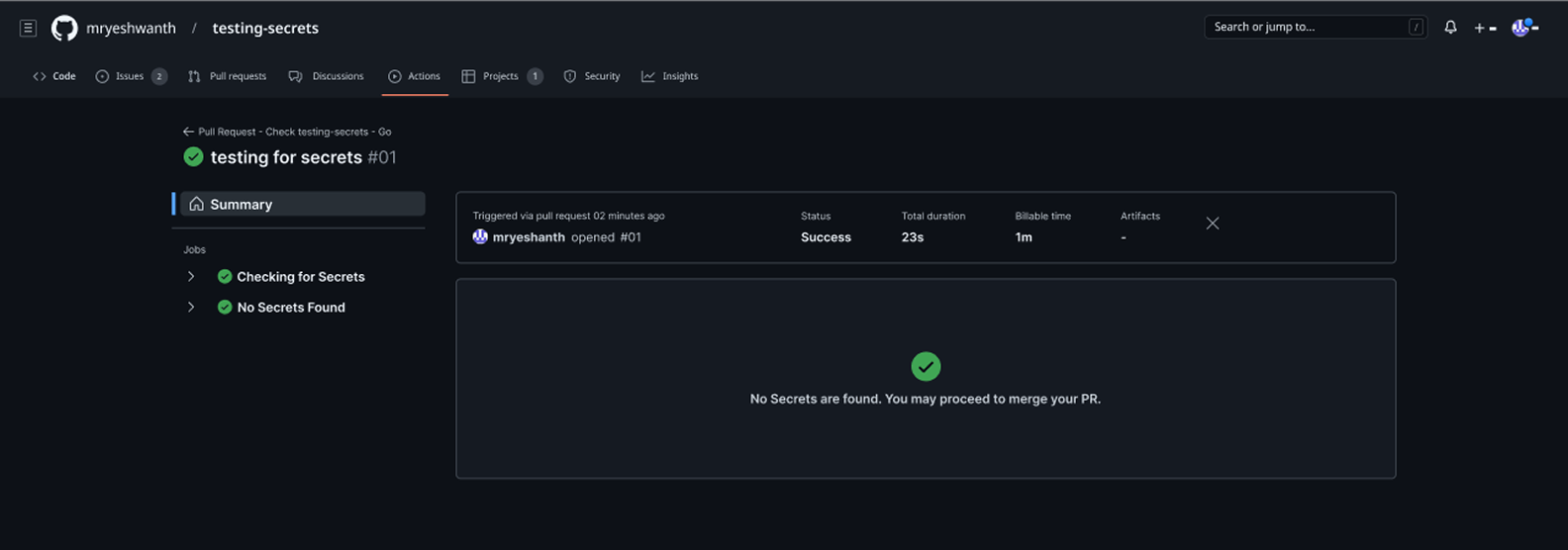
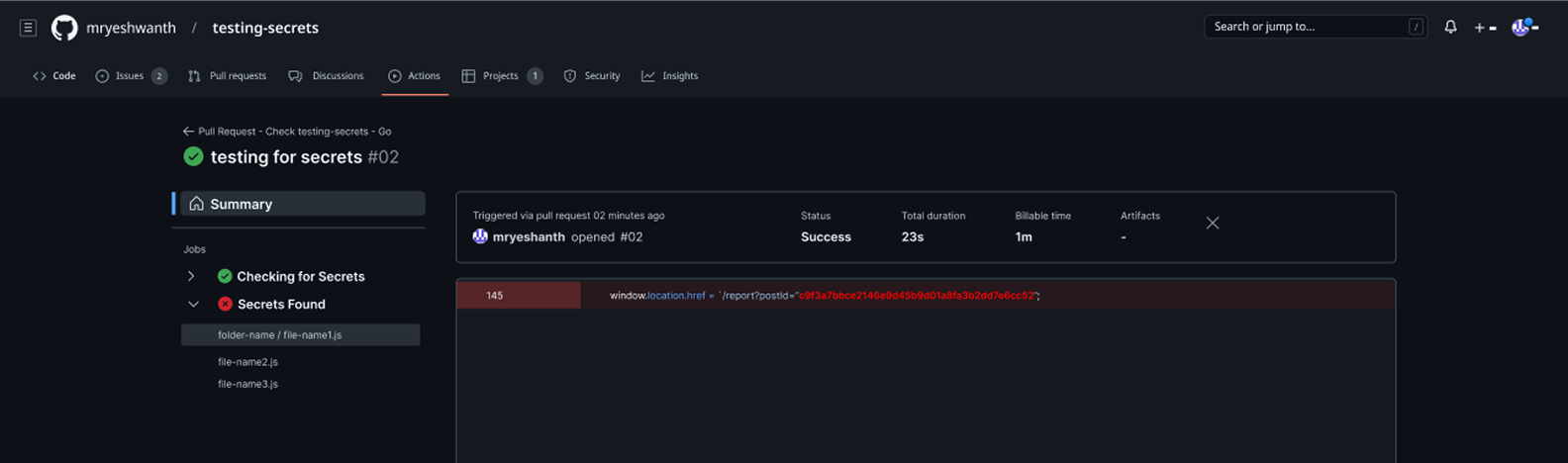
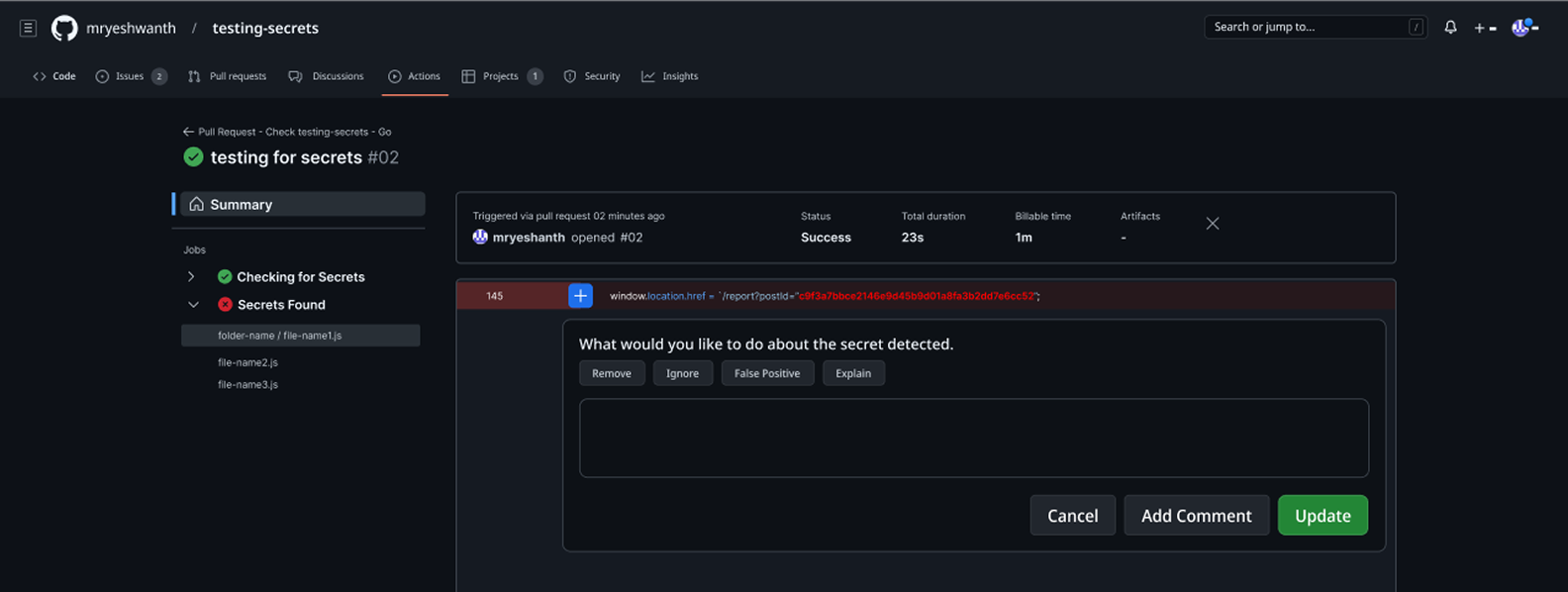
For each detected secret, SecureFlow provides a concise explanation and guided next steps. Developers fix issues in seconds, keeping PR resolution under the 2-minute threshold validated through research.
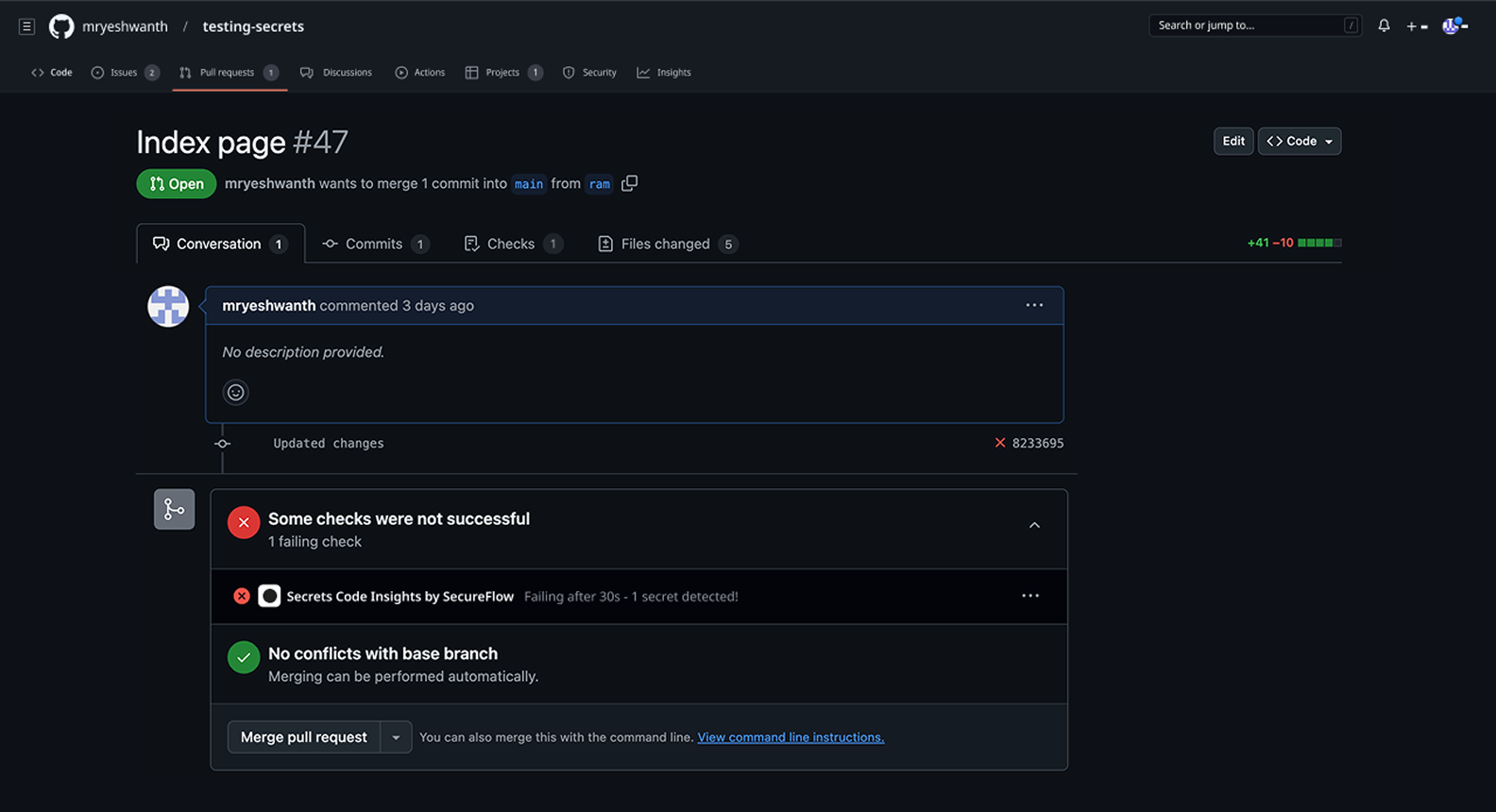
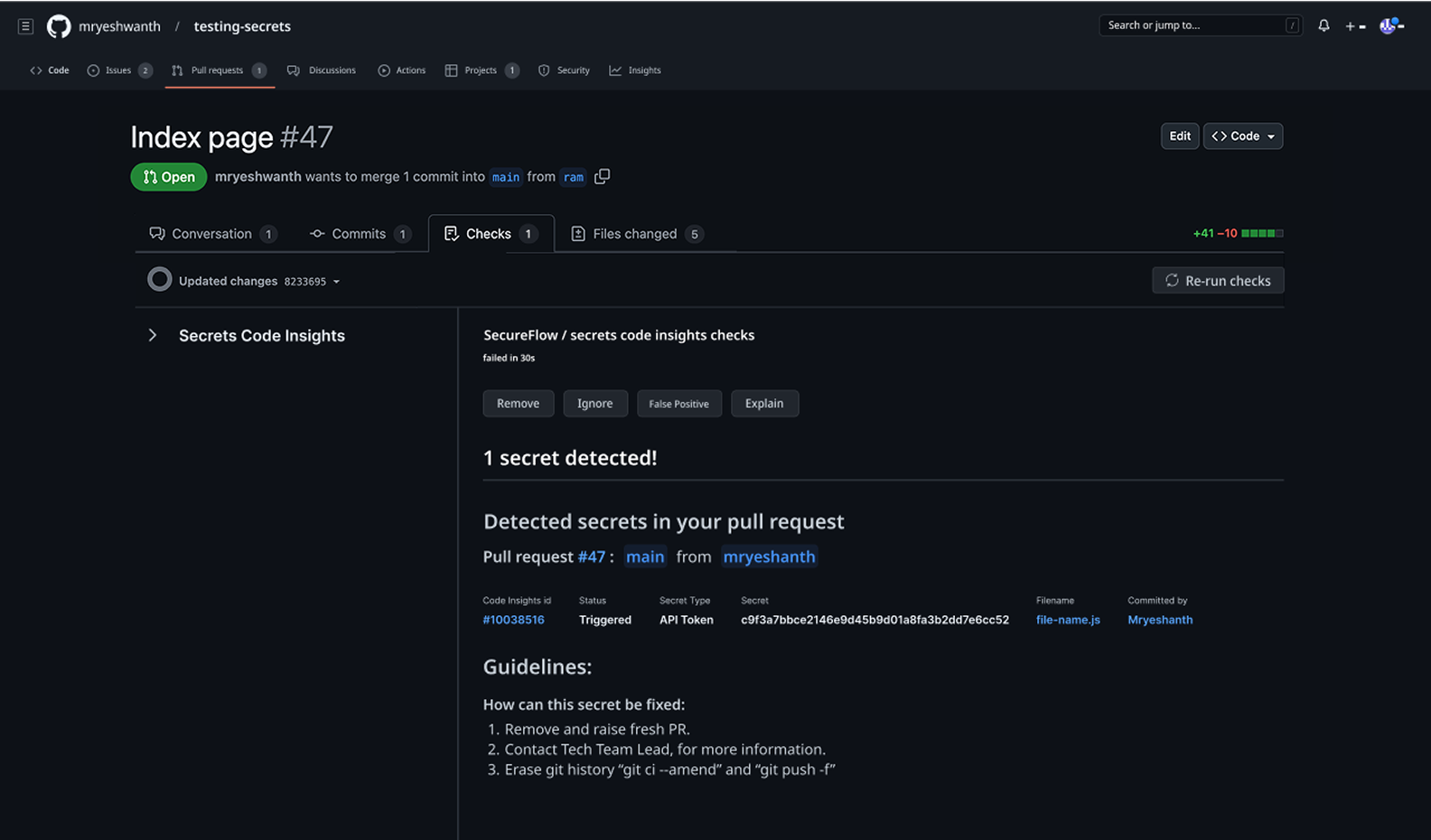
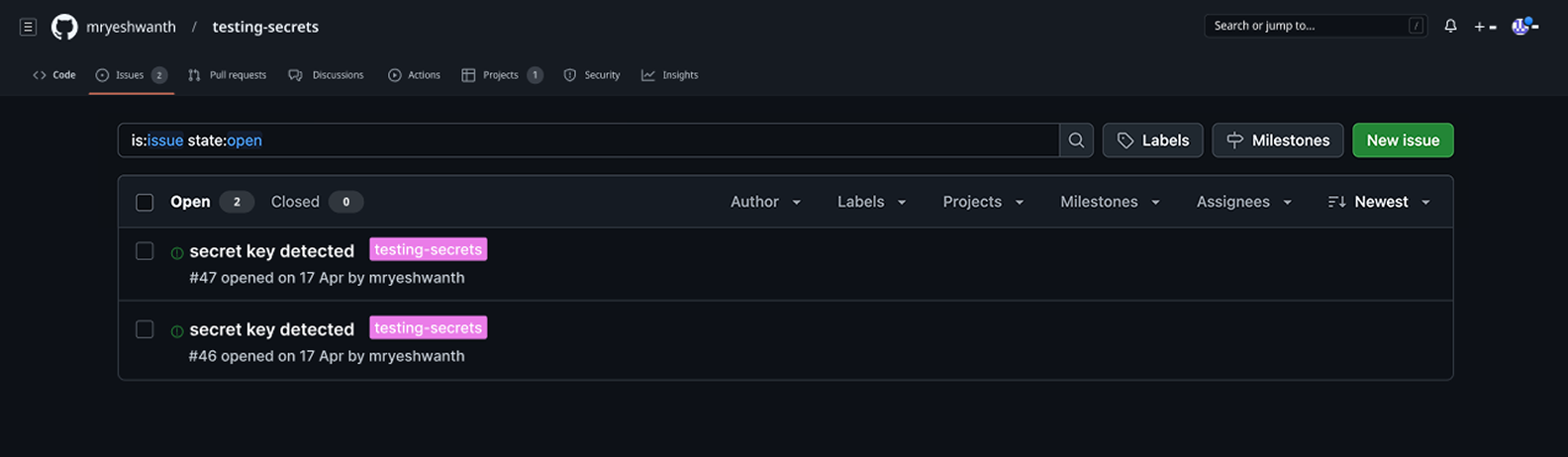
High-risk secrets are automatically converted into GitHub issues with remediation instructions, ensuring they are properly tracked and never lost inside conversations.
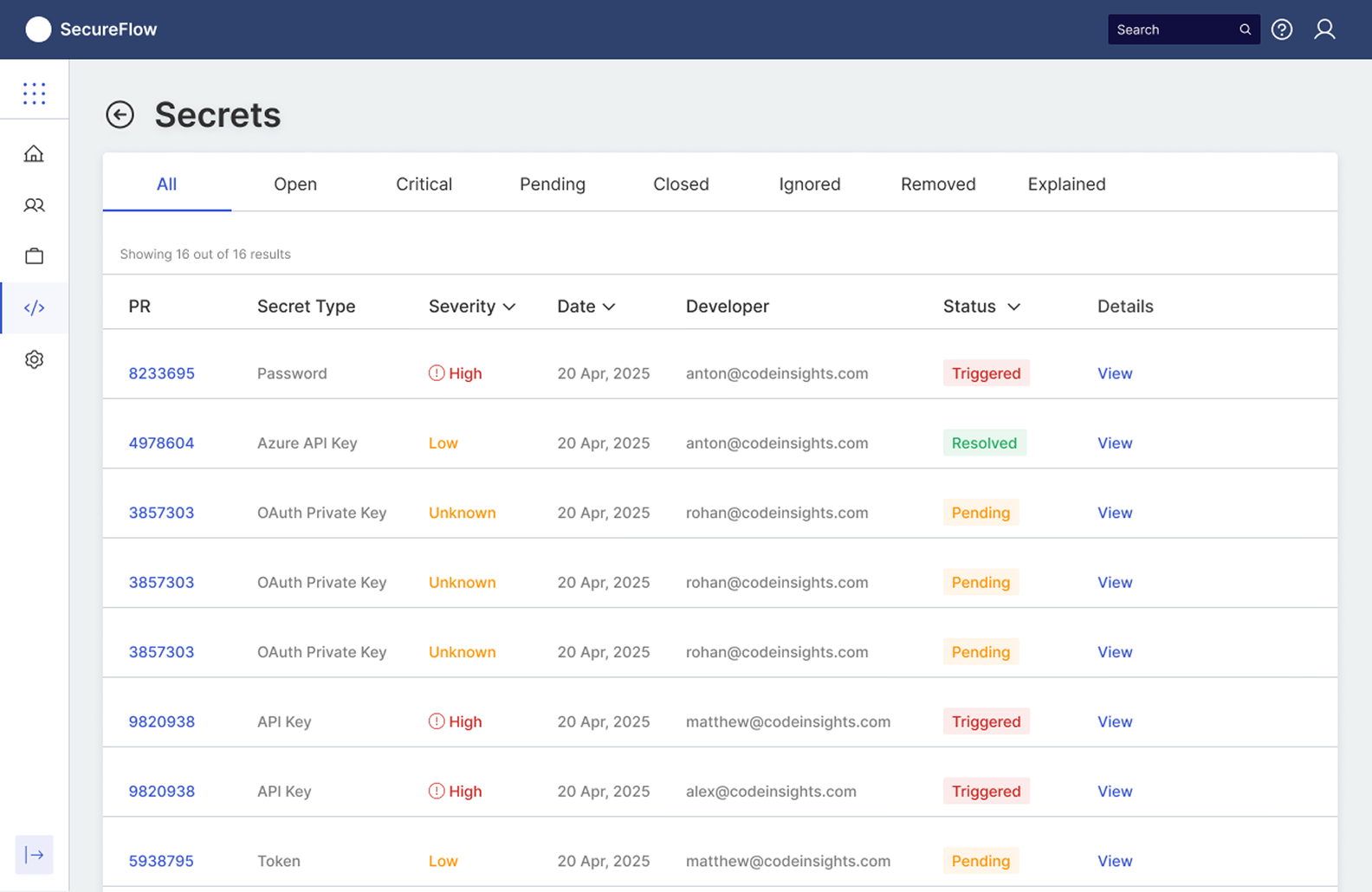
A focused dashboard highlights:
This enables coaching and oversight without micromanagement, turning security into a measurable, teachable team habit.

Engineering initially favored a standalone dashboard, simpler to build and maintain. I argued for inline GitHub integration using research data: 5 of 6 developers said they would ignore any tool requiring them to leave their PR workflow. I prototyped both approaches with the tech lead and tested them with developers. The inline approach won decisively: developers resolved issues 4x faster without context-switching.
I also navigated tension with the security team, who wanted aggressive blocking (prevent merge until all secrets resolved) versus developers who needed flexibility. I designed a tiered severity model: critical secrets block merge, medium-risk secrets warn but allow merge with acknowledgment, low-risk patterns are informational only. This satisfied both security requirements and developer autonomy.
When issues go unresolved past a threshold, SecureFlow escalates to team leads. I designed this flow around coaching, not punishment. The system surfaces teachable patterns and context around why the issue occurred, helping leads mentor their team and reduce repeated mistakes.
42% reduction in unresolved secrets
22% improvement in secret remediation rates
17% reduction in pull request review time (from an average of 8 minutes to 6.5 minutes per PR)
50% reduction in security-related rollbacks
The initial false-positive dismissal flow was too cumbersome. Developers had to write a justification for every 'Mark as False Positive' action. In the first week, developers just ignored alerts instead. I simplified it to a one-click dismiss with an optional note, and added a weekly digest for team leads to review dismissed alerts in batch. Dismissal compliance went from 20% to 42%.
For the team lead dashboard, I designed it from scratch around three questions: What is at risk now? Who needs coaching? Are we improving? This focus kept the dashboard actionable from day one without the need for a later simplification.
This project fundamentally shaped how I design for highly technical users. Three hard-won principles:
SecureFlow reinforced my belief that the best developer tools are invisible. They protect, they inform, and they get out of the way. Success is not whether developers love the tool. It is whether they stop thinking about security breaches because the system handles it.
Led the end-to-end redesign of claims processing over 2 months. Positioned AI as an assistant, not an automator. Designed a unified workspace with suggest-and-confirm patterns that cut processing time while maintaining agent trust.